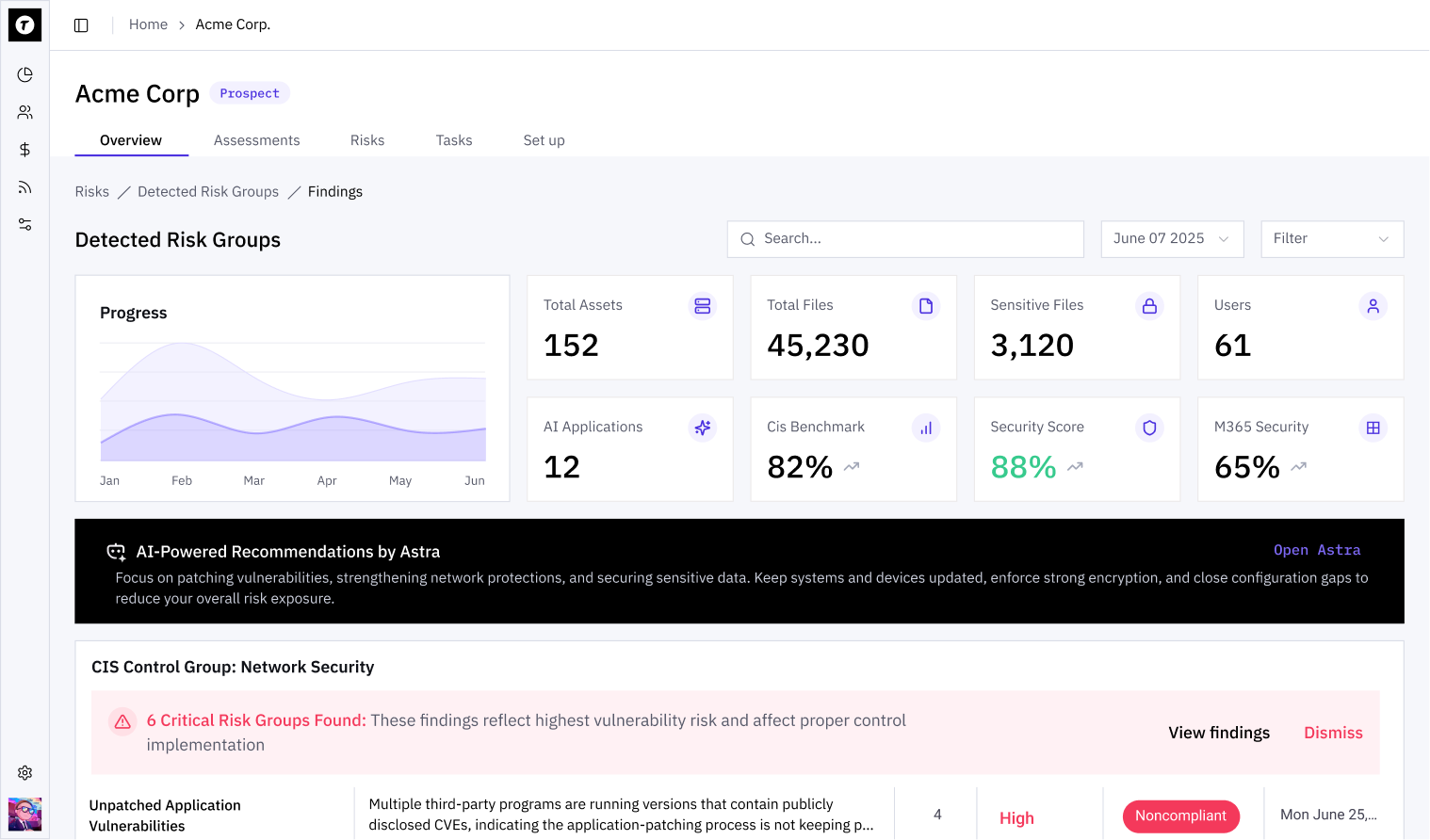
Continuously Manage Risk From Endpoint to Cloud
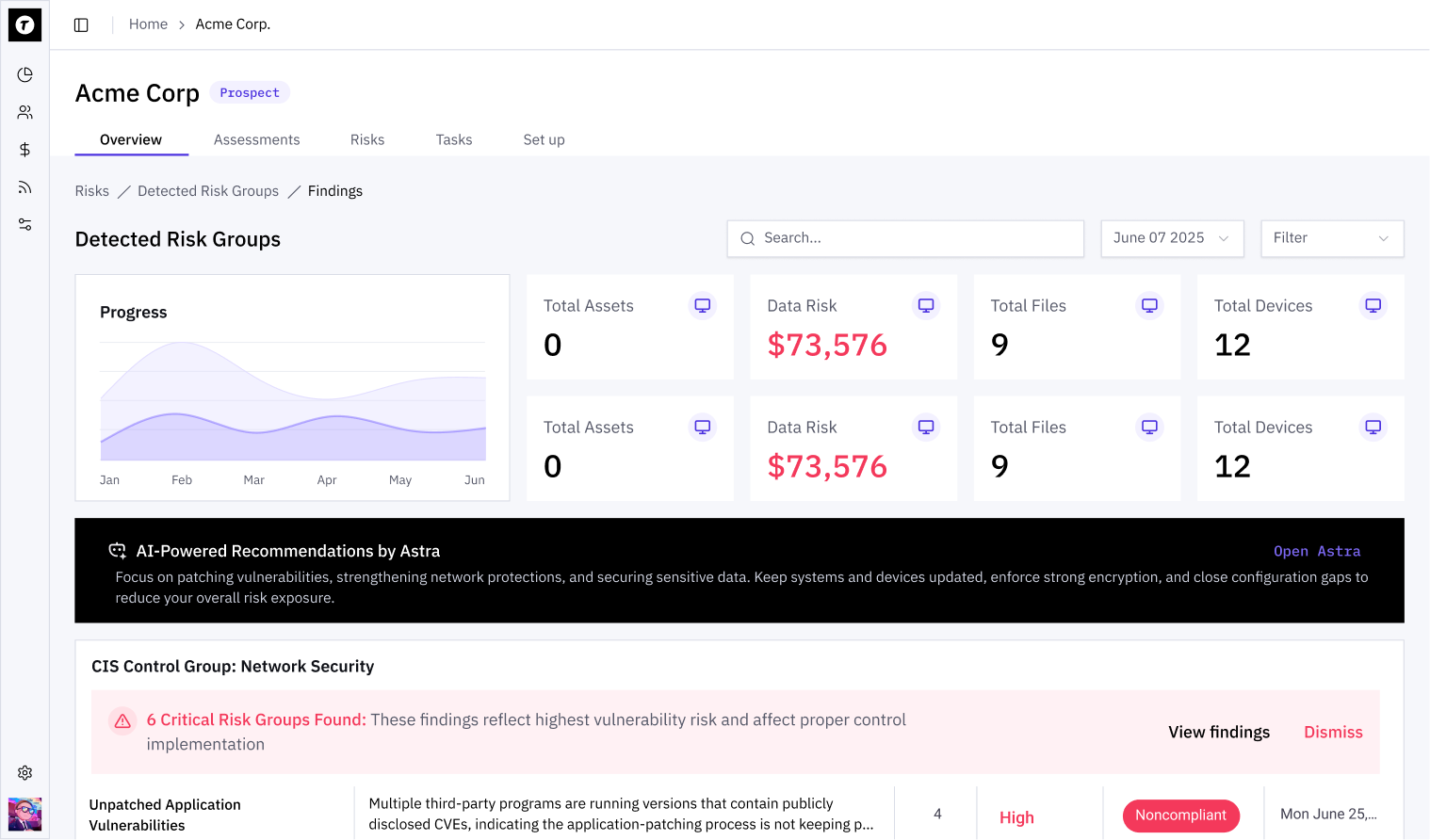
Monitor assets, prioritize vulnerabilities, and document remediation aligned to CIS controls.
You Don’t Grow Out of Risk. You Grow Into It.
As your clients scale, their attack surface expands and so does your exposure. Their top-line revenue becomes part of your risk equation.
Open ports and exposed services create liability
Credential reuse & dark web exposure increase risk
MFA gaps and cloud misconfigurations go unnoticed
MSPs are increasingly named in breach litigation
Clients expect documented security programs
Clients expect documented security programs
Vulnerability exposure changes daily, your management approach must be continuous
Gain Complete Visibility Across Your Client Base
Monitor network, endpoint, cloud, and SaaS assets in real time.
Find the gaps. Fix what matters.
Not all vulnerabilities carry equal risk.
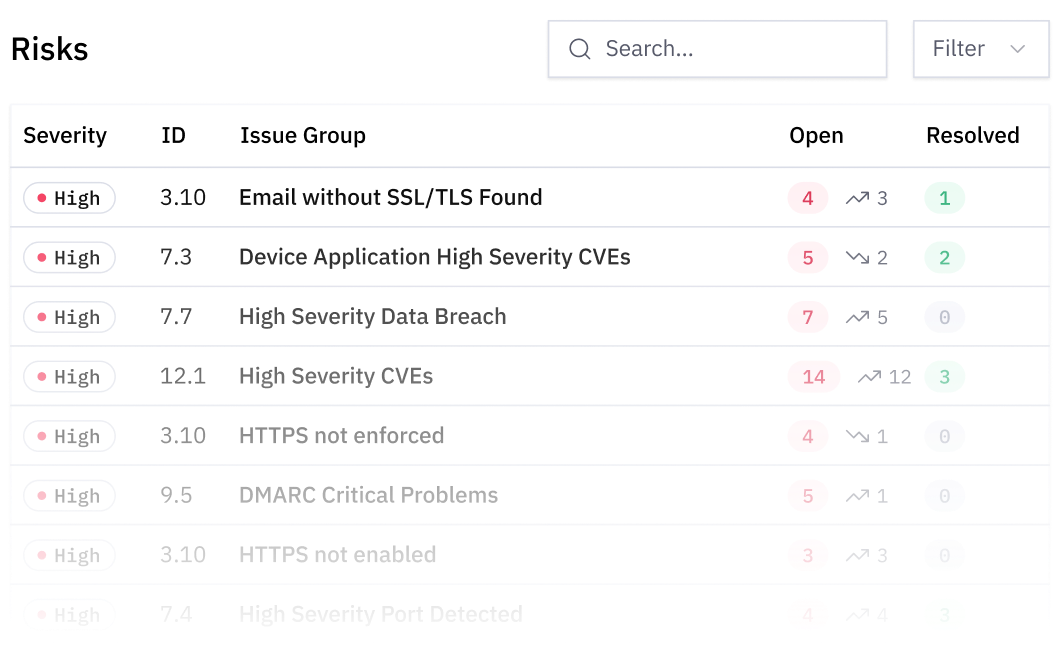
Move beyond CVSS severity alone. Act on real-world exposure.
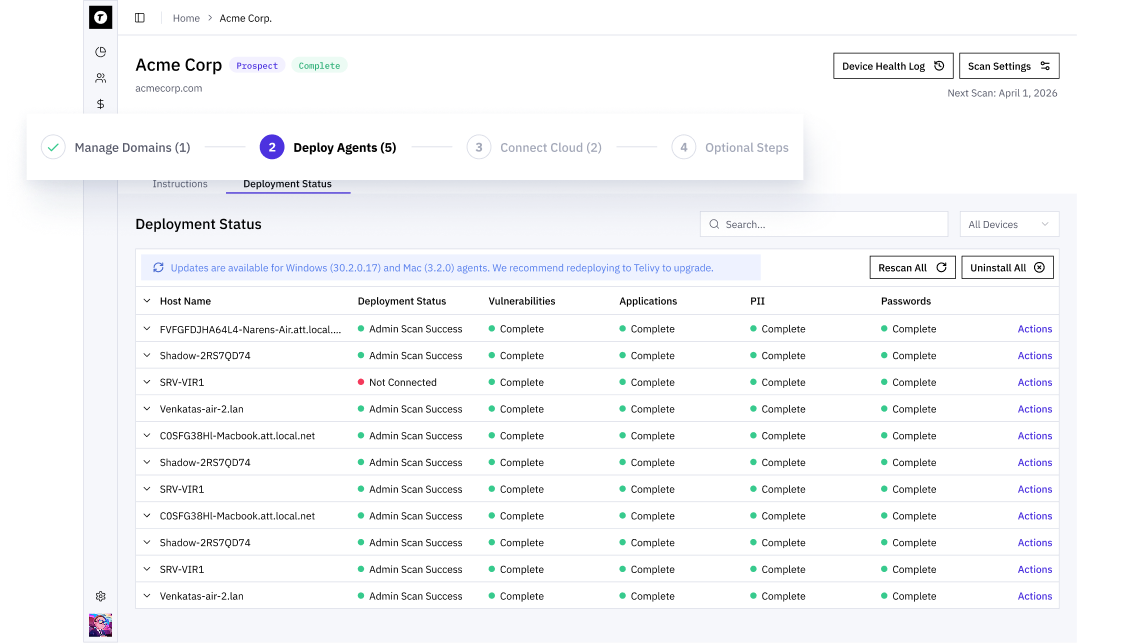
Turn Findings Into Action
POA&M & Remediation Tracking
Generate structured plans of action automatically and track progress over time.
PSA/RMM Integration
Push remediation tasks directly into your service workflows.
Drift & Change Monitoring
Track posture changes and validate that gaps are actually closed.
Automated Remediation (Tier 3)
Where integrated enforcement exists, control changes update posture automatically — not just in documentation, but in practice. Remediation is connected to control enforcement across the platform.
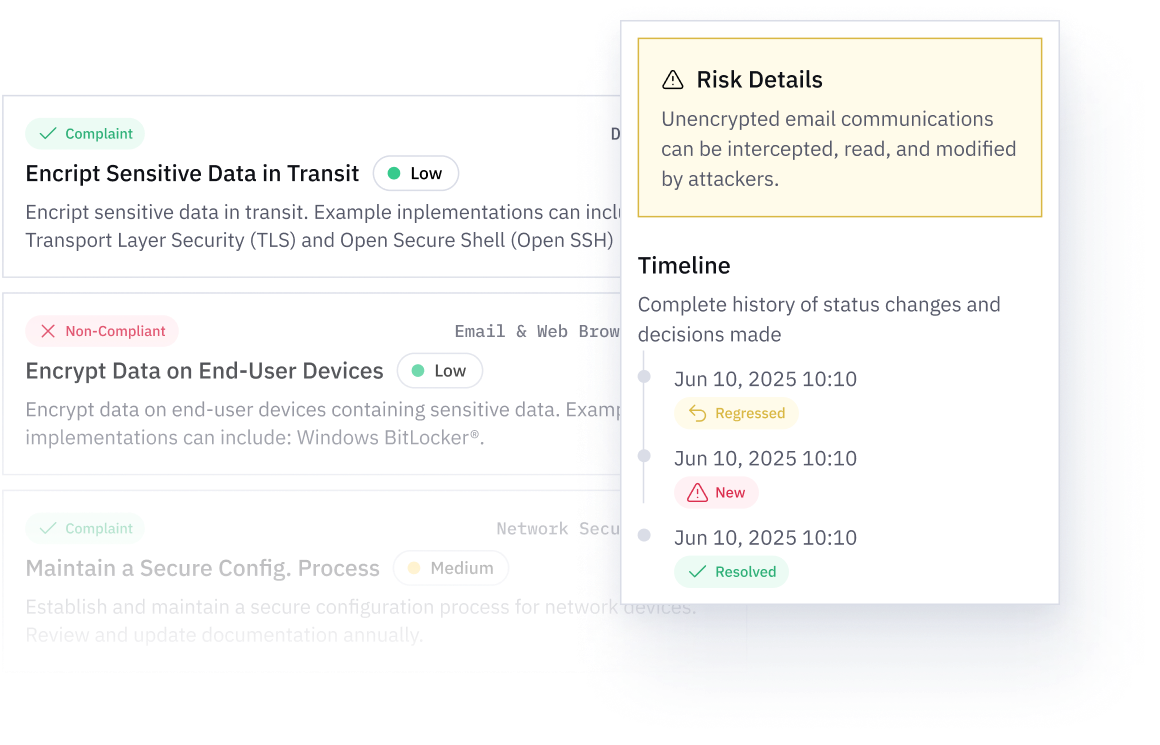
Built for Technical Safe Harbor
Protect Your Business with Continuous Monitoring and Defensible, Framework-Aligned Remediation.
Demonstrate structured risk management across every client.
Command Stronger Client Conversations
Telivy provides:
Turn technical findings and activity into measurable risk reduction.
Designed for MSP Operations
Telivy
Traditional Scanners
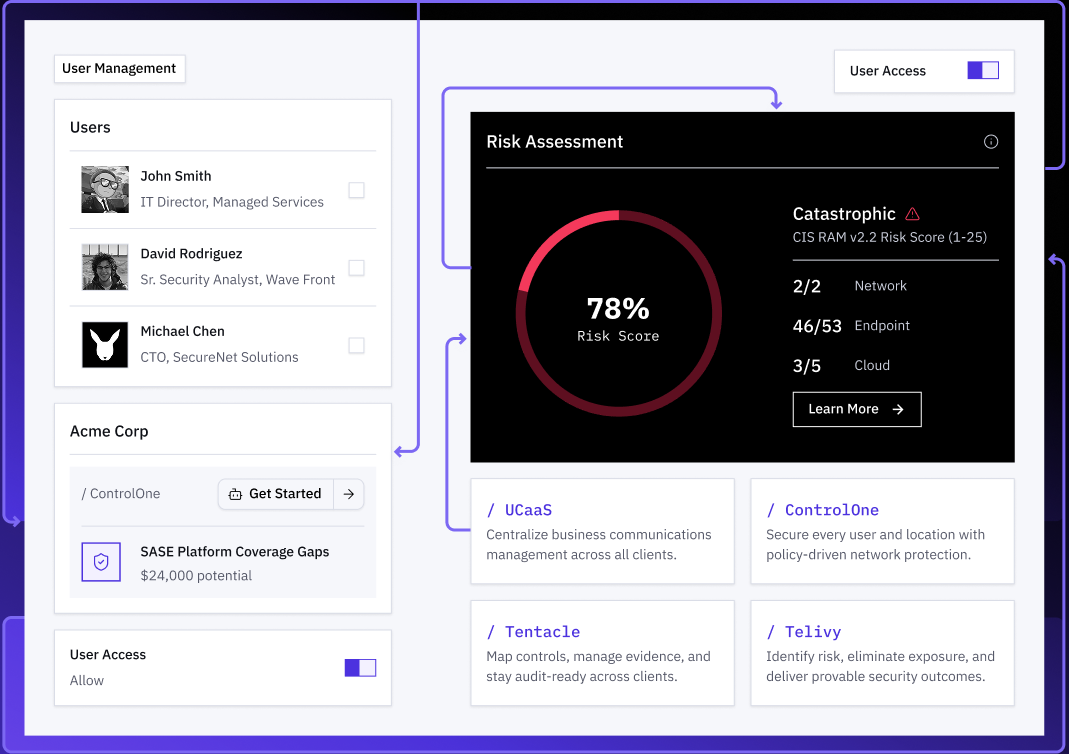
Part of a Unified Risk Platform
Telivy does not operate in isolation.
Protect Your Clients. Protect Your Business.
Continuously manage risk, document remediation, and strengthen your technical posture.
